1/6 🐀 DiscordRAT 2.0 – When Discord Becomes a Command Center
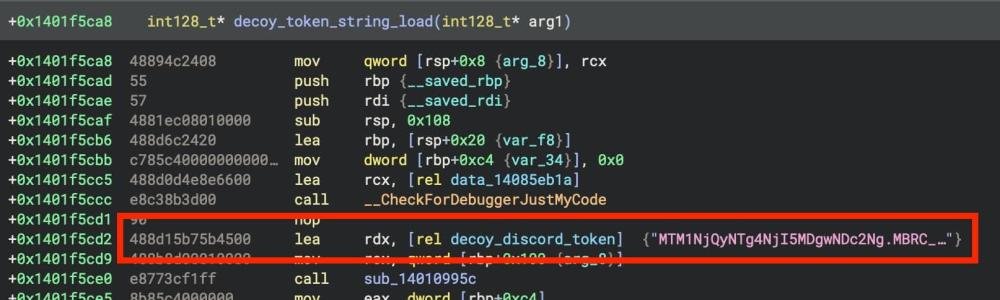
DiscordRAT 2.0 is a Remote Access Trojan (RAT) that uses as its command-and-control channel.
Instead of connecting to suspicious servers, it communicates through Discord, making detection harder.
2/6 ⚙️ How It Operates
Once installed on a victim’s system, DiscordRAT connects to a hidden Discord bot.
Attackers can then remotely control the infected computer through Discord commands — silently and instantly.
It blends with normal Discord traffic.
3/6 🔥 What Attackers Can Do
• Monitor victim activity
• Access files and folders
• Capture screenshots
• Log keystrokes
• Steal credentials
• Execute remote commands
Full system control — from anywhere.
4/6 🎯 Why It's Hard to Detect
DiscordRAT is dangerous because:
• Uses trusted Discord servers
• Traffic appears legitimate
• No obvious malicious server connection
• Bypasses basic firewall rules
It hides in plain sight.
5/6 🚨 Common Infection Methods
Attackers spread it through:
• Fake cracked software
• Malicious downloads
• Phishing links
• Fake game mods or tools
• Social engineering
One careless download is enough.
6/6 🛡️ How to Stay Protected
• Avoid downloading untrusted files
• Use updated antivirus protection
• Monitor unknown background processes
• Enable firewall protection
• Be cautious with Discord downloads
Your awareness is your strongest defense.
DiscordRAT 2.0 is a Remote Access Trojan (RAT) that uses as its command-and-control channel.
Instead of connecting to suspicious servers, it communicates through Discord, making detection harder.
2/6 ⚙️ How It Operates
Once installed on a victim’s system, DiscordRAT connects to a hidden Discord bot.
Attackers can then remotely control the infected computer through Discord commands — silently and instantly.
It blends with normal Discord traffic.
3/6 🔥 What Attackers Can Do
• Monitor victim activity
• Access files and folders
• Capture screenshots
• Log keystrokes
• Steal credentials
• Execute remote commands
Full system control — from anywhere.
4/6 🎯 Why It's Hard to Detect
DiscordRAT is dangerous because:
• Uses trusted Discord servers
• Traffic appears legitimate
• No obvious malicious server connection
• Bypasses basic firewall rules
It hides in plain sight.
5/6 🚨 Common Infection Methods
Attackers spread it through:
• Fake cracked software
• Malicious downloads
• Phishing links
• Fake game mods or tools
• Social engineering
One careless download is enough.
6/6 🛡️ How to Stay Protected
• Avoid downloading untrusted files
• Use updated antivirus protection
• Monitor unknown background processes
• Enable firewall protection
• Be cautious with Discord downloads
Your awareness is your strongest defense.